Data Security: Protecting Your Business and Your Clients
Data security isn’t just a technical requirement—it can protect your business as well as your clients! From federal regulations to industry standards, understanding your responsibilities is the first step toward building a secure and trustworthy company.
Federal Trade Commission (FTC) Compliance
Under the Safeguards Rule, financial institutions must protect the consumer information they collect. It is vital to learn if your business is considered a “financial institution” under the Rule. If so, have you taken the necessary steps to comply?
Many companies collect personal information from their customers, including:
- Names, addresses, and phone numbers
- Bank and credit card account numbers
- Income and credit histories
- Social Security numbers
The Gramm-Leach-Bliley (GLB) Act requires companies defined as “financial institutions” to ensure the security and confidentiality of this information. As part of its implementation of the GLB Act, the FTC issued the Safeguards Rule, requiring measures to keep customer information secure.
“Safeguarding customer information isn’t just the law—it also makes good business sense. When you show customers you care about their security, you increase their confidence in your company.”
The definition of a “financial institution” includes many businesses that may not normally describe themselves that way. The Rule applies to all businesses, regardless of size, that are “significantly engaged” in providing financial products or services. This includes:
- Check-cashing businesses and payday lenders
- Mortgage brokers and nonbank lenders
- Personal property or real estate appraisers
- Professional tax preparers and courier services
For more details, the Rule is available at ftc.gov.
NIST – Information Security Fundamentals
The Information Technology Laboratory (ITL) at the National Institute of Standards and Technology (NIST) promotes the U.S. economy and public welfare by providing technical leadership for the Nation’s measurement and standards infrastructure.
Small businesses are an important part of our nation’s economic and cyberinfrastructure. Consider these statistics:
- There are approximately 28.2 million small businesses in the United States.
- Small businesses produce roughly 46% of our nation’s private-sector output.
- They create 63% of all new jobs in the country.
While security might not always be the highest priority for a small business, a single cybersecurity incident can be detrimental to customers, employees, and business partners. It is vitally important that each small business understands and manages the risk to information, systems, and networks.
IRS – Protecting Taxpayer Information is the Law!
Data thefts at tax professionals’ offices are on the rise. Identity thieves are placing tax practitioners firmly in their sights to file fraudulent tax returns. Data security is now a necessity for every tax professional, from sole practitioners to large firms.
Key responsibilities for tax professionals include:
- Education: Every employee, including administrative staff, should be educated about security threats.
- FTC Compliance: Tax return preparers must create and enact security plans to protect client data. Failure to do so may result in an FTC investigation.
- Online Standards: Providers must follow the security and privacy standards in Publication 1345, Handbook for Authorized IRS e-file Providers.
Protecting taxpayer data is good business. Theft may result in a loss of reputation, a loss of clients, or a loss of money. Consider engaging security professionals for assistance or checking with your professional liability carrier about data theft coverage.
How can we help?
ITNEXT has the experience and knowledge to help protecting your business.
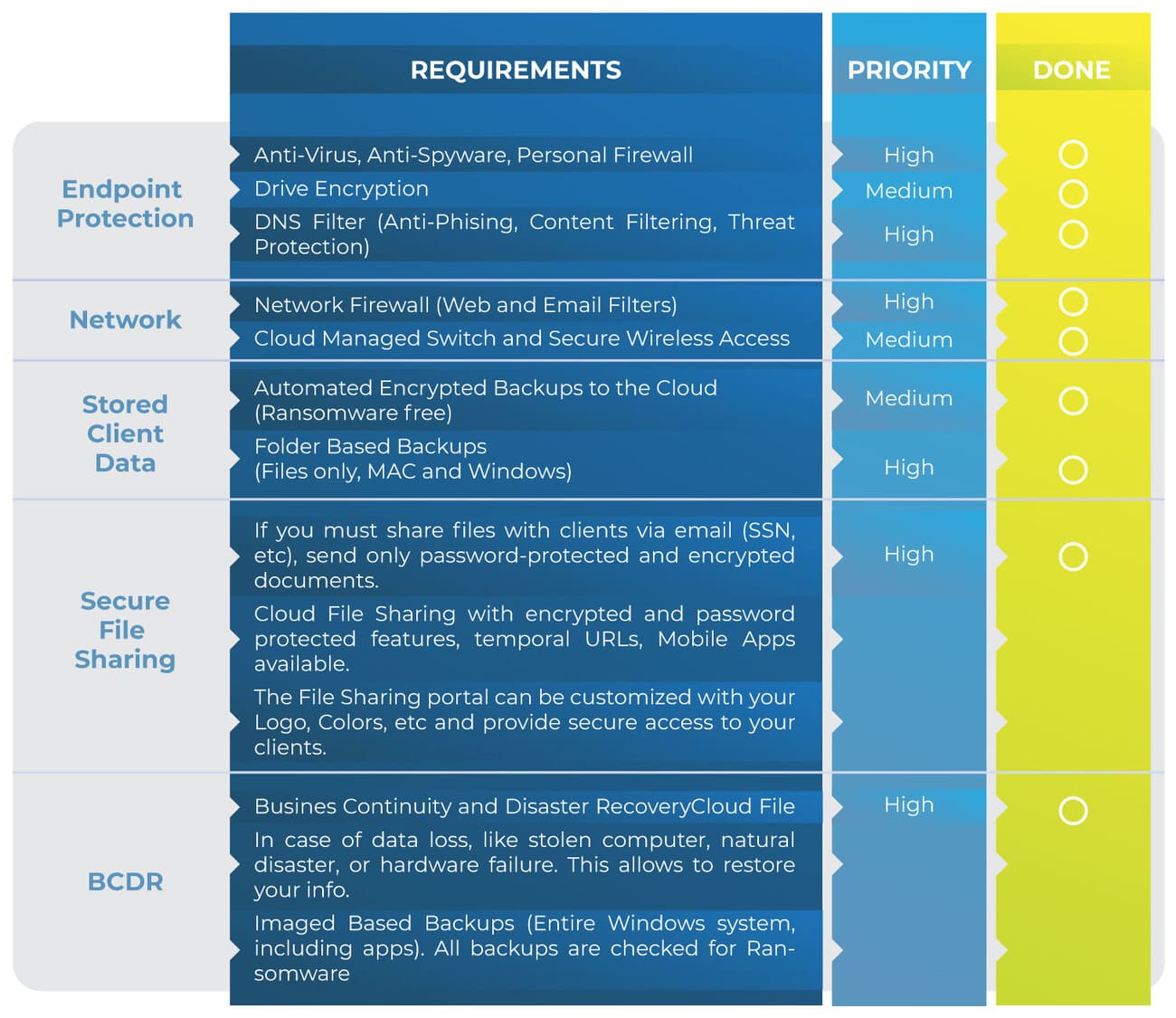
We’ve built a checklist of all requirements specified by the IRS, NIST, and FTC in order to make it easy for our customers. We’ve leveraged key enterprise technologies and strategies to make it affordable to Small-Medium Businesses.
We provide enterprise-level security infrastructure through our partnerships with the most recognized vendors in the industry. We know one solution does not fit all customer’s needs, and that is the reason why we have come up with a checklist that can be mapped to different technologies from different providers.
We, as consultants, our job is to determine the best strategy based on your needs.